SNMP is the main protocol for monitoring network hardware which may be used in Zabbix — an all-in-one solution for monitoring a large number of objects in static (changing slowly) networks.
The earlier versions of the protocol—SNMPv1 and SNMPv2—had security vulnerabilities that led to attacks and data breaches. In order to protect sensitive data, SNMPv3 should be enabled.
I’ll demonstrate how to configure SNMPv3 in Zabbix to monitor network hardware, how to create proper templates in Zabbix, and what you can achieve by organizing a distributed alert system in a large network.
About SNMPv3
SNMP is the main protocol for monitoring network hardware used to monitor network devices and to manage them by sending simple commands (for example, to reboot a device, to enable or disable network interfaces, etc.).
The main difference between SNMPv3 and the previous versions — the classic security functions [1-3]:
- authentication, which allows us to determine if a request came from a trusted source;
- encryption, which prevents any third party from reading data if it is intercepted in transit;
- integrity, which helps to ensure that a data packet hasn’t been tampered with during transit.
SNMPv3 allows using security models where different users and user groups have an authentication strategy assigned to them (while, in a request from a server to a monitored device, the previous versions of SNMP only checked the community string, which was transmitted as plain text and served as a password).
SNMPv3 also introduces security levels that define acceptably secure device settings and SNMP agent behavior. The combination of a security model and a specific level determines which security mechanism will be used to process an SNMP data packet [4].
Combinations of security models and levels in SNMPv3
| Level | Authentication | Encryption | What Happens |
| noAuthNoPriv | Username | No | Authentication with a username (strongly not recommended) |
| authNoPriv | Message Digest Algorithm 5 (MD5) or Secure Hash Algorithm (SHA) | No | Authentication based on Hashed Message Authentication Code (HMAC)-MD5 or HMAC-SHA (not recommended) |
| authPriv | MD5 or SHA | Data Encryption Standard (DES) or Advanced Encryption Standard (AES) | Authentication based on HMAC-MD5 or HMAC-SHA + encryption based on DES or AES (best practice) |
How to
To monitor a network device, we must set up SNMPv3 both on the server and the monitored device.
Setting up network device
- The basic Cisco network device configuration in the CLI:
1. Define a group of SNMPv3 users (‘snmpv3group‘), the access mode (‘read‘), and access privilege for the ‘snmpv3group‘ to view certain branches of the device’s MIB tree.
snmp-server group snmpv3group v3 priv read snmpv3name
2. Define the user — ‘snmpv3user‘, the user group — ‘snmpv3group‘, and state authentication based on MD5 (with’md5v3v3v3‘ as the password) and encryption based on DES (with ‘des56v3v3v3‘ as the password).
snmp-server user snmpv3user snmpv3group v3 auth md5 md5v3v3v3 priv des des56v3v3v3
NOTE. It is preferable to use AES. DES here is used as an example only.
NOTE. When defining a user, Access Control List can be added to specify IP addresses of servers that can monitor this device.
3. Define codename (‘snmpv3name‘) for specific branches of MIB tree so that ‘snmpv3group‘ could access them. ISO, instead of limiting it to a single branch, allows ‘snmpv3group‘ to access all MIB objects of the monitored device.
snmp-server view snmpv3name iso included
- The basic Huawei network device configuration in the CLI:
snmp-agent mib-view included snmpv3name iso snmp-agent group v3 snmpv3group privacy read-view snmpv3name snmp-agent usm-user v3 snmpv3user group snmpv3group snmp-agent usm-user v3 snmpv3user authentication-mode md5 md5v3v3v3 snmp-agent usm-user v3 snmpv3user privacy-mode des56 des56v3v3v3
Setting up access
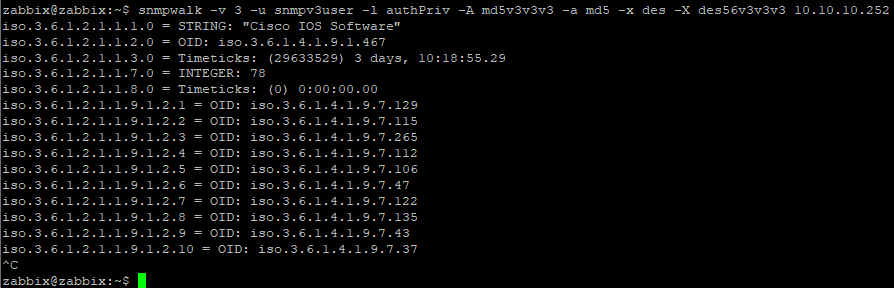
After network devices are configured, to ensure that the monitoring server can access them by SNMPv3, you can run ‘snmpwalk‘:
snmpwalk -v 3 -u snmpv3user -l authPriv -A md5v3v3v3 -a md5 -x des -X des56v3v3v3 10.10.10.252
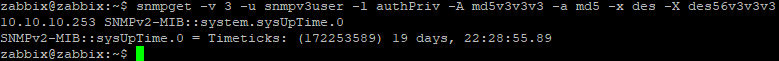
To request specific objects, you can also run ‘snmpget‘, which relies on MIB files and gives a more concise output:
Configuring an item to use SNMPv3
We need to configure a standard item that will use SNMPv3 on the Zabbix template level. The simplest way is to use MIB-independent numerical forms of OIDs.
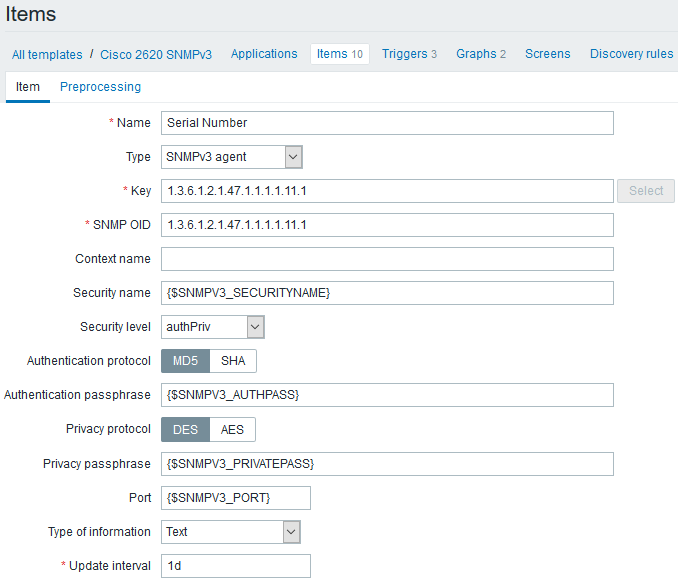
Data elements
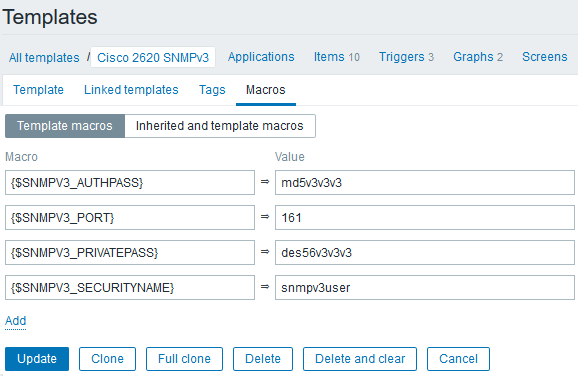
You can use user macros since they will be the same for every template item. If all of your network devices have the same SNMPv3 parameters, macros are defined on a template level, otherwise — on a host level.
Templates
NOTE. Keep in mind that the monitoring system has usernames and passwords for authentication and encryption only. The user group and access to MIB objects are defined on each monitored device.
Zabbix Polling template
It is recommended to make any polling templates as detailed as possible:
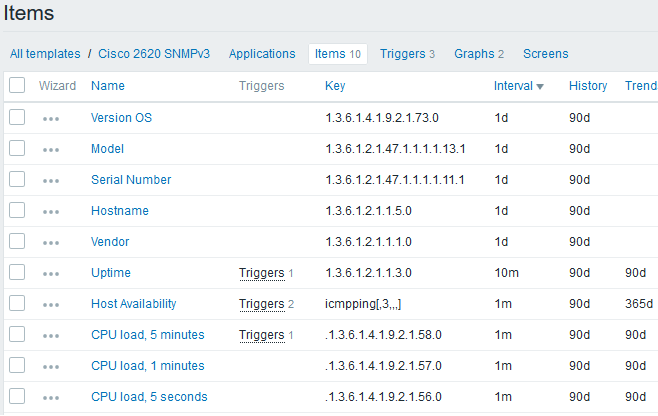
Polling template
Configuring triggers
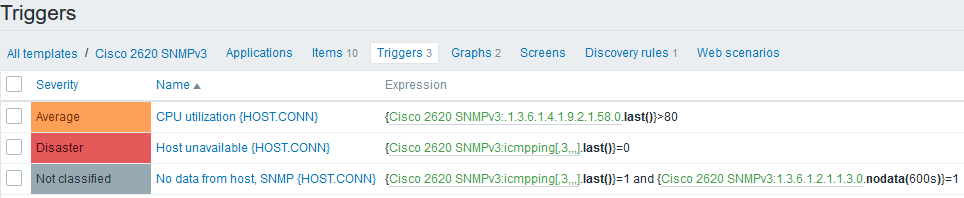
Triggers
If trigger names include a system macro {HOST.CONN}, alerts on the dashboard would display not only device names but also their IP addresses.
SNMP may be used to determine whether a device is not available, besides a regular echo request.
Sometimes a device responds only to ICMP requests, which may mean that different devices have the same IP address because of firewall or SNMP settings. Still, you might not get all monitoring data to investigate a network incident if you use only ICMP to check host availability.
Network interface discovery
Network interface discovery is the most important monitoring function for networking hardware. Since a single network device can have hundreds of interfaces, we must filter unneeded interfaces out, so that they don’t clutter up the database and data visualization.
Standard discovery function for SNMP with many detectable parameters allows for more flexible filtration:
discovery[{#IFDESCR},1.3.6.1.2.1.2.2.1.2,{#IFALIAS},1.3.6.1.2.1.31.1.1.1.18,{#IFADMINSTATUS},1.3.6.1.2.1.2.2.1.7]
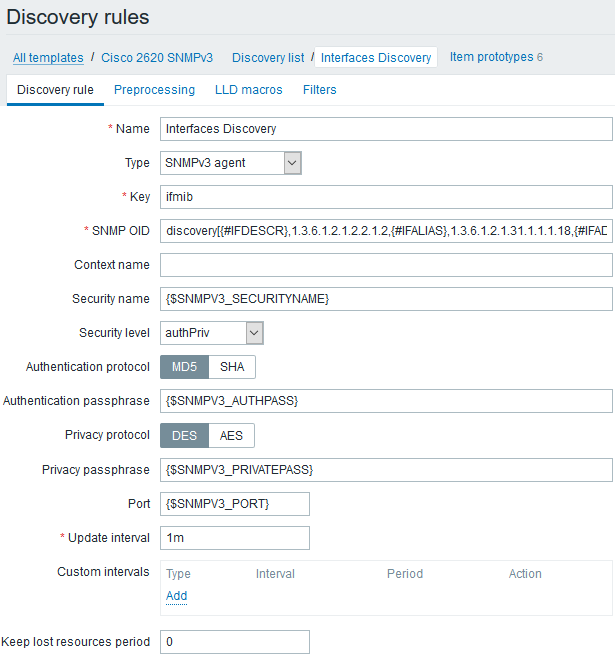
Discovery rules
Network interfaces can be discovered and filtered by their type, user description, and the administrative state of their ports.
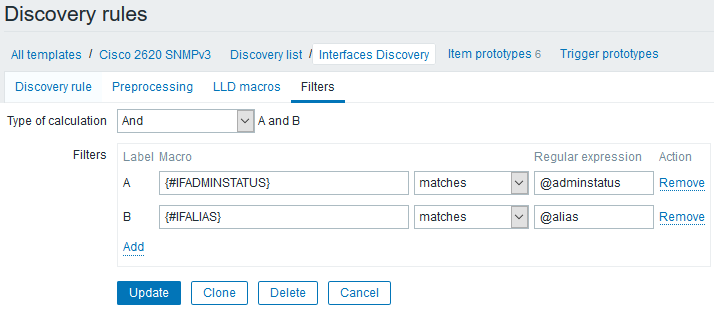
Filters
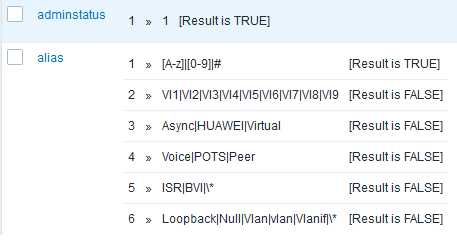
Regular expression
So, excluded interfaces will be those that:
- have been manually disabled (‘adminstatus<>1‘), because of ‘IFADMINSTATUS‘;
- don’t have a text description, because of ‘IFALIAS‘;
- have an asterisk (*) in their text description, because of ‘IFALIAS‘;
- are service/technical interfaces, because of ‘IFDESCR‘ (when regular expressions are applied in discovery, one regular expression, alias, will check on both ‘IFALIAS‘ and ‘IFDESCR‘).
Monitoring results
So, we’ve got a list of network devices:
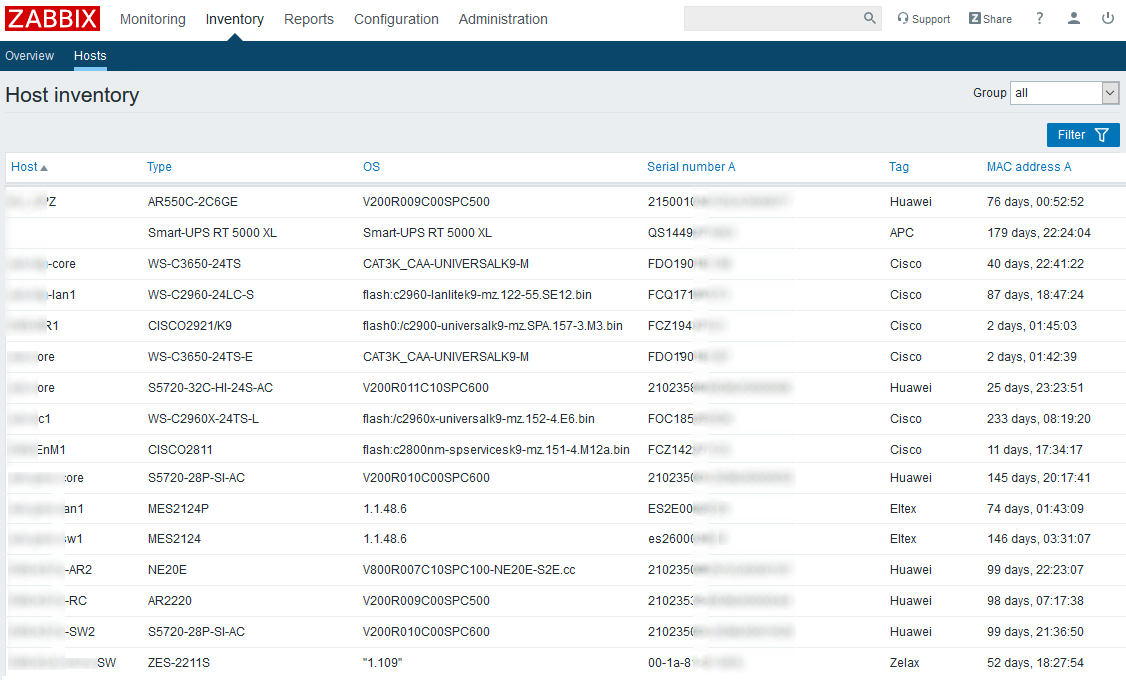
List of network devices
Creating templates for each series of hardware makes analysis of monitoring results more convenient as it allows to see information grouped by series on:
- up-to-date software,
- serial numbers, and
- presence of a janitor in the server room (indicated by low uptime percentage).
Various templates may give different views on your network, for example:
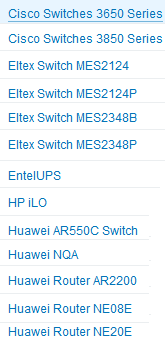 Hardware series templates
Hardware series templates
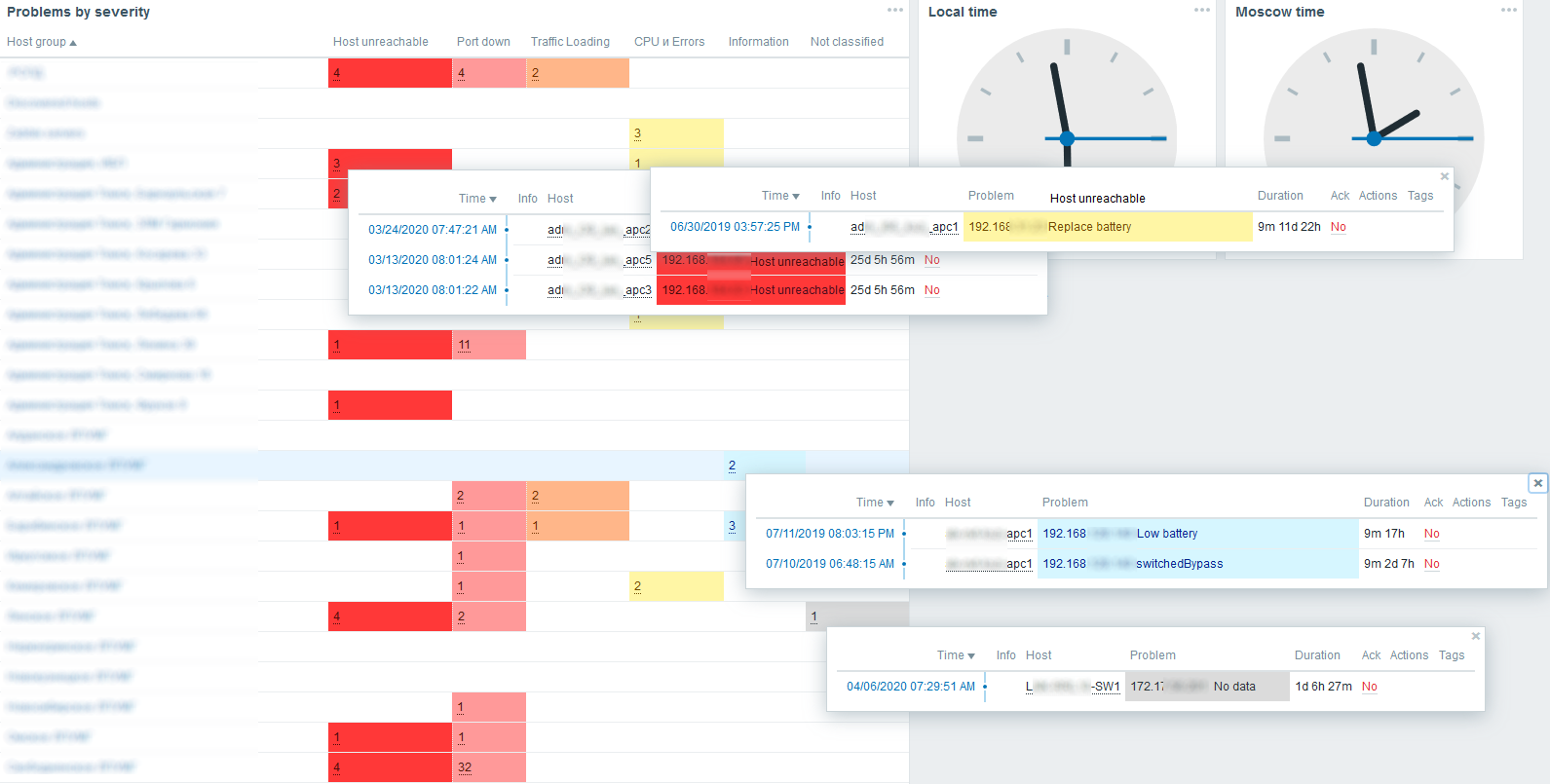
Main monitoring dashboard with triggers divided by level of importance
If you create templates for each device model in your network, your monitoring system can become a tool for forecasting malfunctions and failures (if you have necessary sensors and metrics). Zabbix is a good solution for monitoring network, server, and service infrastructures, and leveraging Zabbix for maintaining network hardware demonstrates the system’s capabilities.
References
- Hucaby D. CCNP Routing and Switching SWITCH 300-115 Official Cert Guide. Cisco Press, 2014. pp. 325-329.
- RFC 3410. https://tools.ietf.org/html/rfc3410
- RFC 3415. https://tools.ietf.org/html/rfc3415
- SNMP Configuration Guide, Cisco IOS XE Release 3SE.
Chapter: SNMP Version 3.
https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/snmp/configuration/xe-3se/3850/snmp-xe-3se-3850-book/nm-snmp-snmpv3.html
The post is translated from the habr.com article.







 Prev Post
Prev Post 




I didn’t find out the template of “MIB-independent numerical forms of OIDs” in my zabbix server, pls help
Hello, Vincent!
Meaning is that you must know the SNMP OID in your device. For monitoring of traffic we are using standart OID’s, for example, 1.3.6.1.2.1.1.5.0 for hostname, or 1.3.6.1.2.1.2.2.1.10.{SNMPINDEX} for inbound traffic on interface (you need to find interfaces by using Low Level Discovery – LLD (tool in zabbix)).
I usually look for rare OIDs on google or using snmpwalk from the zabbix server console.
Sorry for my bad english.
thanks for your replied, but I didn’t find template of “Cisco 2620 SNMPv3” like yours. I tried to find some other templates but no see Type “SNMP v3 agent” like you
All it’s ok, it’s not a problem. You can’t find template of “Cisco 2620 SNMPv3” like mine, because i make my own templates (i’m network engineer). Basic zabbix templates are primitive, they need to be modified to suit your tasks.
SNMPv2 or SNMPv3 – are just monitoring protocols, they are configured in the host (in zabbix and in device). And SNMP OID – metrics, you need to configure it in items into template.
picture for visualization https://drive.google.com/file/d/1peSi4HWJYIUDg5zYm3RXOET96Yluu3aa/view?usp=share_link
few pictures about template https://drive.google.com/file/d/1ClnA5ukFjeYY9audC0gQZCOvJy4n0Hze/view?usp=sharing, https://drive.google.com/file/d/1FWV3aDjruvPzIXTXsdZPFjpmxFJhb-6M/view?usp=sharing, https://drive.google.com/file/d/1RxaUS3y4r-NfMRjTx6OOk3oGXKtrHLzc/view?usp=sharing, https://drive.google.com/file/d/1Z1p8QllYgv3hEpNjANBGDzem63K4ORwG/view?usp=sharing, https://drive.google.com/file/d/1fr1KUtMNZwBT24RXlPQeAUzbIyYWGj1c/view?usp=sharing, https://drive.google.com/file/d/1peSi4HWJYIUDg5zYm3RXOET96Yluu3aa/view?usp=sharing
If you need help for monitoring of your network infrastructure, i can help you. If you want to figure it out yourself – make a template as in the article, and everything will work!
I am reaching out to inquire if you could kindly share the SNMP v3 templates specifically designed for Huawei and Juniper devices. We are in the process of implementing SNMP v3 monitoring for these devices and would greatly appreciate any templates or configuration guidance you could provide to ensure smooth integration with Zabbix.
Your support in this matter would be highly valued, and we look forward to your response. Please let me know if you need any further details from our end.
Thanks, I setup successfully SNMPV3 in zabbix, it is little bit than “items” picture above
It is perfectly!
Have a good day!
foe cisco and huawei devices?
Not very clear. Why is the setting shown on the device, and then immediately moved on to macros, OID and Items? It is not clear how to add the device itself to Zabbix, because the Context name and Security name fields are completely absent in Cisco terminology.
I did everything as described in the post, it works on Cisco Prima, but not on Zabbix. There is ping from Zabbix to the device.
Сommand from Zabbix server