Any business, big or small, might become a target of DoS attacks or intrusion attempts at some point, which is a serious risk to consider. In order to tackle that issue, the ISO (International Standardization Organization) created a set of rules for companies to follow, thus improving the safety and quality of operations.
Among those, the ISO/IEC 27005 was made as a facility for a satisfying Information Security implementation from a Risk Management approach. According to the standard, Risk is defined as:
Risk is the effect of uncertainty in objectives. It is associated with the potential in which threats may explore vulnerabilities of an active and consequently damage an organization.
Vulnerabilities found on servers, for example, can be quickly identified and dealt with thanks to monitoring tools. The ISO/IEC 27005 developed controls and guidelines for monitoring from where we can highlight the following:
“… constant monitoring is necessary so changes can be detected.”
Where can Zabbix help in Risk Management?
With proactive monitoring using ZABBIX, some risks can be avoided, below we list two examples:
Ransomware attack in servers
A known threat among security teams is ransomware. Ransomware is known as malicious code that when executed encrypts data on a host, followed by demands a fee for decryption (usually in bitcoin).
The most common ways ransomware can propagate are:
- Exploitation of a vulnerability in an unpatched system.
- Through unfiltered firewall ports.
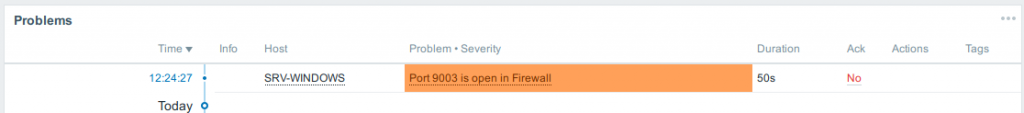
With Zabbix, the Information Security team can be proactive in ransomware detection by, for example, monitoring if the WSUS server has the latest updates, set up warnings for uncommonly opened ports, alert on known ransomware process execution, etc. In the following example, we’ve set up Zabbix to send alerts when ports used by ransoware wannacray (9003, 9101 and 9001) are opened on the firewall:
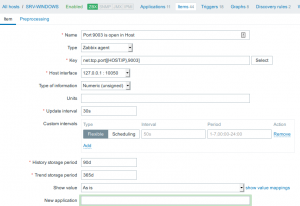
Configuring such an alert in Zabbix is very easy simply by using the net.tcp.port key. In order to do so, you need to go the Configuration > Host> Item and click Create Item.
Set the Name, Type, and Key as in the example:
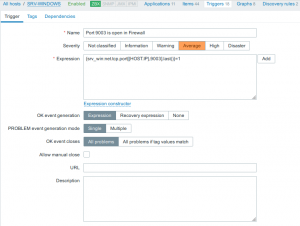
Now we need to create a Trigger. In Host navigate to Trigger > Create Item. Set the Name, Severity, and Expression:
The exact expression we used is:
{srv_win:net.tcp.port[{HOST.IP},9003].last()}=1
Click add and Finish.
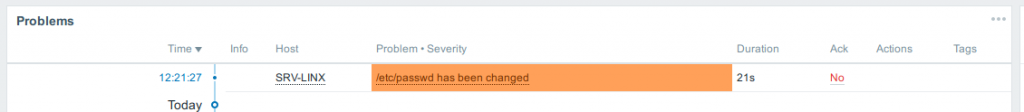
Changes in files
In some cases, intruders modify operating system’s sensitive files such as logs, users, passwords or service configurations.
Monitoring the integrity of files is of utmost importance and Zabbix can address that by verifying checksums:
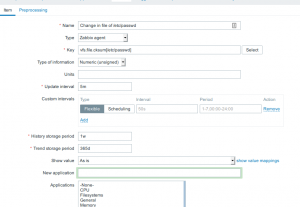
Configuring this in Zabbix is fairly trivial via the use of the vfs.file.cksum key. To do this, simply go to Configuration > Host> Item and click Create Item.
 Set the Name, Type, and Key as the following example:
Set the Name, Type, and Key as the following example:
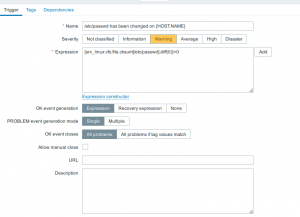
We will, of course, need to create a Trigger as well, so head to Trigger > Create Item. Set the Name, Severity and Expression as in the example:
Here’s the expression we used:
{srv_linux:vfs.file.cksum[/etc/passwd].diff(0)}>0
Click add and Finish.
You can start by writing simple checks like in the examples above and then evolve the approach as necessary. As is often the case, however, Zabbix community is here to share their full-featured threat control solutions like this.
No matter what you prefer, deep customization or out-of-the-box solutions, Zabbix can give you both thanks to its flexibility and active community.
Conclusion
In order to comply with ISO 27005 some organizations make use of Zabbix as a monitoring solution of choice for their servers, firewalls, cloud and overall infrastructure. With all that Zabbix supports the information security staff in decision making and proactive identification of anomalies, that might occur in the infrastructure.






 Prev Post
Prev Post